Redpoint Cyber™ Services: Redpoint Labs™
How do you stop cyber criminals or state-sponsored actors before a breach materializes? You need to be proactive and vigilant. Our team keeps your organization secure through a unique approach to target, pursue and eliminate threats on your network - We Hunt the Hunter®!

Hunt The Hunter™
Breach Detection
The Threat Landscape Has Changed
Traditional endpoint and network security products simply aren’t enough to protect the modern enterprise. After all, most of these offerings have just expanded on the same frameworks that hackers have successfully exploited for years. So what do you do? You hunt, or be hunted.
A Different Way
In a security environment that is ever-changing, the best way to stay on top of potential threats is to start throwing punches. Our “collect-and-analyze” approach to active threat detection makes hackers earn every inch of their access.
Working in tandem, our persistence detection agent and threat mitigation team significantly reduce the time of detection, destroying malicious footholds as soon as they are created.
Machine Learning and Forensic Security Experts
An unbeatable combination. Redpoint Cybersecurity’s platform, which doesn’t require installation or network reconfiguration, uses algorithms to scan and “ethically” attack enterprise networks. It performs exploits like remote execution, password cracking, malware injection and privilege escalation without disrupting service. This enables the retesting and validation of novel remediation actions. A dashboard shows steps in simulated attack vectors, as well as a summary of recommended mitigation steps our clients need to take.
Hunt the Hunter®: We fight to secure your company!
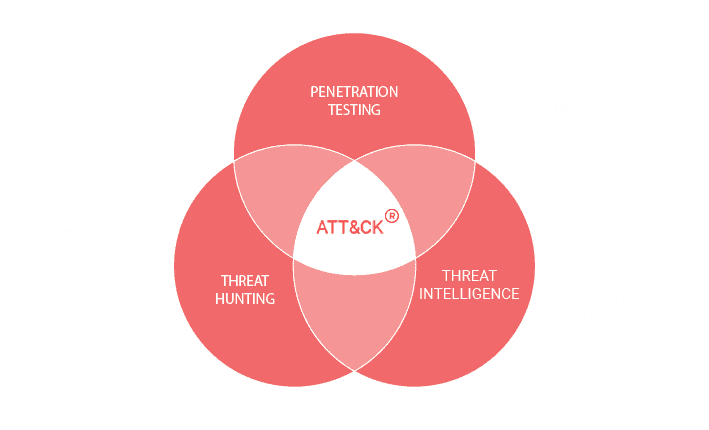
Redpoint Labs is precise, thorough and experienced to help define your threat visibility, neutralize threats keeping you one step ahead of the most sophisticated cyber threat actors.